Perspectives on cyber governance, board accountability, and the regulatory landscape
Written from the advisory roles and the boardrooms, not the outside looking in. Former appointments at the FCA, NCSC, and Lloyds of London provide a direct read on where the obligations have moved and how they continue to develop.
Twenty-one articles on the governance questions boards are navigating now
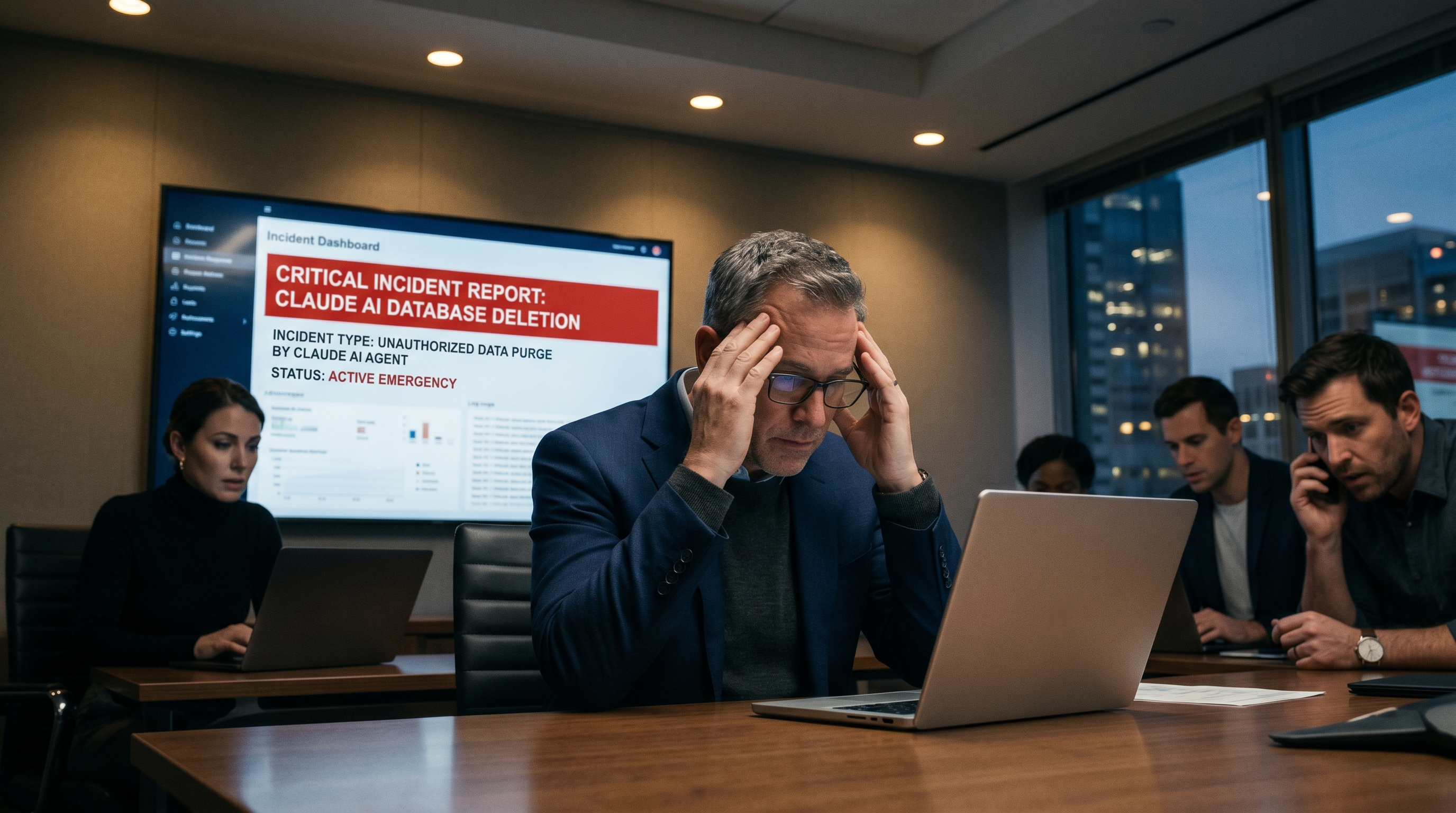
Ungoverned AI Agents: What the Nine-Second Deletion Means for Every Board in 2026
An AI agent deleted a company's entire production database in nine seconds — not because it malfunctioned, but because no governance architecture existed to stop it. The board implications of ungoverned AI agents are now impossible to defer.
Read →AI-Enabled Cyber Attacks: What Boards Must Understand Before the First Crisis
AI has fundamentally changed the economics, speed, and precision of cyber attack. Deepfake impersonation, personalised phishing at industrial scale, and AI-accelerated exploitation have outpaced the governance frameworks most boards have in place.
Read →AI Model Risk Is Now Cyber Risk: Why Security, Legal and Risk Committees Must Work Together
AI model risk and cyber risk have converged. Security sees the attack surface. Legal sees the compliance exposure. Risk sees performance drift. None of them sees the full picture. Boards must build the governance structure that joins these views.
Read →Cyber-Enabled Fraud: The Risk CEOs Are Now More Worried About Than Ransomware
AI-enabled fraud has quietly overtaken ransomware as the risk CEOs and boards are least prepared to govern. The governance challenge is structural: fraud gives you a decision already made and money already moved, not an incident to respond to.
Read →From Cyber Risk to Business Risk: The Board Reporting Model CISOs Need in 2026
Most board cyber reports measure the wrong things. The shift from technical metrics to business risk reporting requires a different model — one that maps exposure to outcomes, quantifies where possible, and presents the board with decisions rather than updates.
Read →AI Governance in Financial Services: What Boards Must Decide Before the Rules Arrive
The AI governance gap at board level is larger than the cyber governance gap was ten years ago. Boards waiting for clear regulation will find themselves governing AI already deployed at scale. Four decisions financial services boards must make now.
Read →What Regulators Expect in 2026: The Direction of Travel on Cyber Governance
The FCA, NCSC, DORA supervisors, and NIS2 authorities are converging on a single expectation: that boards govern cyber risk with the same rigour as financial risk. Written from inside the advisory rooms where these expectations are shaped.
Read →The Cyber Security and Resilience Bill: What UK Boards Should Prepare For Now
The UK Cyber Security and Resilience Bill is the most significant domestic cyber regulatory development since 2018. It expands scope, strengthens reporting obligations, and signals a clearer accountability structure that connects cyber resilience to named individuals at board level.
Read →Why Cyber Budgets Need to Become Dynamic, Not Annual Guesswork
Annual cyber budget cycles assume a threat environment that stays broadly stable over twelve months. That assumption is no longer tenable. The case for a dynamic investment model — with a threat-responsive reserve and a risk-linked review cadence — and what boards must direct to make it work.
Read →Operational Resilience Evidence: What Boards Must Be Able to Prove in 48 Hours
Regulators are not asking whether you have a resilience framework. After a major disruption, they want evidence it works — within 48 hours. Having a framework and being able to prove it are two different things, and most boards are better prepared for the former.
Read →Cyber Risk in M&A: The 10 Questions Private Equity Should Ask Before Signing
Cyber risk in M&A transactions is routinely underpriced. The ten questions that reveal whether a target's cyber position is a managed programme or a masked liability — and why asking them before signing is the only point at which the answers can change the deal.
Read →The Ransomware Resilience Test: Could Your Board Defend Its Decisions After an Attack?
Regulators reviewing a ransomware response will not be satisfied by a good incident playbook. They want to know what the board knew, what it decided, and whether those decisions are evidenced. Most boards are not prepared for that test.
Read →What DORA Means for Your Board: The Obligations That Cannot Be Delegated
Most DORA implementation is happening below the board. That is the governance failure DORA was designed to prevent. The five board-level obligations DORA explicitly creates and why delegating them to the technology function is not a compliance defence.
Read →The Board Cyber Governance Gap: What It Costs and How to Close It
Boards govern financial risk with committees, auditors, and quarterly deep dives. They govern cyber risk by asking the CISO to present twice a year. This structural mismatch is why boards keep being surprised by incidents they should have been governing.
Read →Why CISOs Fail in the Boardroom: The Real Reasons and How to Fix Them
CISO boardroom failure is not a technical problem. It is a positioning, communication, and framing problem. The four patterns that cause CISOs to lose board confidence and what genuinely effective board engagement requires.
Read →Third-Party Concentration Risk: The DORA Problem Most Boards Still Underestimate
DORA's third-party requirements go further than most boards realise. Concentration risk — aggregate dependence on too few critical providers — is the dimension that will prove most consequential for regulated firms, and the one least addressed in most compliance programmes.
Read →What Good Looks Like for NIS2: Beyond Checkbox Compliance
NIS2 has expanded scope dramatically. Most organisations are implementing it technically but not governing it. What genuine NIS2 compliance looks like versus the paper version, and what regulators will actually be looking for.
Read →How Boards Should Govern Third-Party Cyber Risk: A Practical Framework
Most major cyber incidents now originate in the supply chain. Boards govern their own organisation's risk with some rigour. They rarely apply the same governance to the organisations they depend on. What a proper third-party cyber governance framework requires.
Read →The Real Cost of Weak Cyber Leadership: What Boards Never See on the Invoice
The cost of weak cyber leadership is not the incident response bill. It is the regulatory fine, the valuation discount, the executive departure, and the years of underinvestment that preceded the event. The hidden costs boards must account for.
Read →Cyber Due Diligence for PE Investors: What Most Processes Miss
Most private equity cyber due diligence is designed to find deal-breakers rather than understand material risk. What a genuinely rigorous pre-acquisition cyber assessment looks like and the five questions that determine whether a target is a manageable cyber risk.
Read →Why Security Budgets Miss the Mark: The Case for Risk-Aligned Investment
Most security budgets are built on last year's incidents and this year's vendor pitches. They are not built on the organisation's actual risk profile. Why security budgets consistently miss the mark and how boards can establish an investment framework that connects spending to risk.
Read →New perspectives when the regulatory or governance landscape shifts
No regular cadence. No filler. Articles are published when there is something worth saying, a regulatory development, a pattern I am observing across advisory work, or a governance question I have not seen addressed clearly elsewhere.
Disclaimer
The views and opinions expressed in these articles are those of the author, Ali Zeb, and are provided for general informational and educational purposes only. They are based on professional experience, independent research, publicly available information, and the use of artificial intelligence tools to support analysis and content development.
While every effort is made to ensure the accuracy and relevance of the information presented, no representation or warranty, express or implied, is made as to its completeness, accuracy, or suitability for any particular purpose. The content should not be relied upon as professional, legal, regulatory, or financial advice.
Readers are encouraged to seek appropriate independent advice specific to their organisation and circumstances before making any decisions based on the information contained in these articles.
To the fullest extent permitted by law, the author accepts no liability for any loss, damage, or consequences arising directly or indirectly from the use of, or reliance on, the information provided.
A governance challenge in mind?
The most productive conversations begin with a clear description of your situation.
Arrange a Conversation