How Boards Should Govern Third-Party Cyber Risk: A Practical Framework
By Ali Zeb · January 2025 · 8 min read
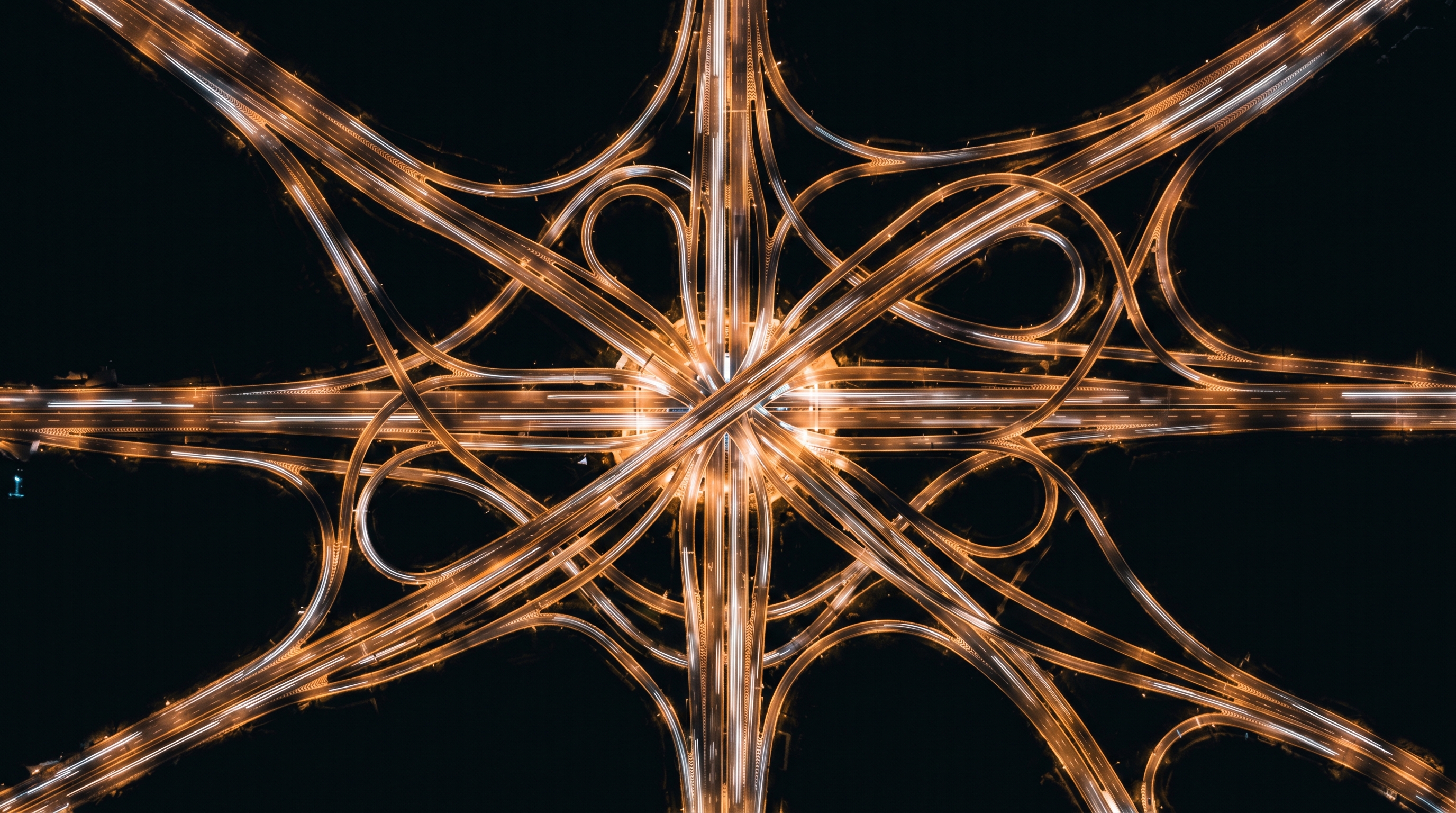
The majority of significant cyber incidents that have affected large organisations in recent years did not begin inside those organisations. They began in a supplier, a technology provider, a managed service partner, or a software vendor that had privileged access to systems and data the target organisation considered its own. The attack surface of a modern organisation extends well beyond its own perimeter, and yet the governance applied to the security of third-party relationships remains, in most boardrooms, either absent or token.
Boards govern their own organisation's cyber risk, imperfectly in many cases, but with some degree of formal attention. They apply almost no equivalent governance to the organisations their business depends on, organisations that may process their customer data, operate their critical systems, provide their cloud infrastructure, or sit inside their network with administrative privileges. The risk those organisations carry is the organisation's risk, and the board is accountable for it.
NIS2, DORA, and the FCA's operational resilience framework all make this explicit. Regulatory accountability for third-party risk does not end at the organisation's boundary. It follows the risk. A board that cannot describe its most critical third-party dependencies, or the security standards those parties are required to meet, or how compliance with those standards is verified, is not governing a significant portion of the risk it is accountable for.
Why third-party risk is structurally different
Third-party cyber risk is harder to govern than internal cyber risk for reasons that are structural, not just operational. Understanding these reasons is the first step toward a governance framework that actually works.
Visibility is indirect. An organisation has limited ability to audit, assess, or monitor the security controls of its suppliers, particularly its smaller or more numerous suppliers. The information available is typically what the supplier chooses to share: certifications, questionnaire responses, and contractual commitments. None of these are reliable indicators of operational security reality. The gap between what a supplier certifies and what a supplier does is often significant.
Accountability is diffuse. Inside an organisation, the CISO owns security. For third-party risk, ownership is typically split between procurement, which manages the commercial relationship, legal, which manages contractual terms, IT, which manages technical access, and the CISO, who may or may not have authority to require security standards from suppliers. In many organisations, no single person is clearly accountable for whether a critical third party is adequately secure.
Concentration risk is invisible. Organisations often discover only during a crisis that several apparently unrelated systems or services depend on the same underlying technology provider or shared service. The failure of a single cloud provider, a single identity management platform, or a single managed service firm can cascade across an organisation in ways that no individual team anticipated because no one held the aggregate view.
"The attack surface of a modern organisation includes every system its suppliers can reach. Governing only your own perimeter is governing half the problem."
Ali ZebA practical framework for board-level governance
Governing third-party cyber risk at board level does not require the board to audit every supplier. It requires the board to ensure that the organisation has a systematic framework for doing so, and that the framework is working. Four components are essential.
A critical supplier inventory. The board should be able to answer, at any board meeting: which are our twenty most critical third-party relationships from a cyber and operational resilience perspective? Who owns each of those relationships? What security standards are they required to meet? When were those standards last verified? The absence of a maintained, board-visible critical supplier inventory is the first governance failure in third-party risk.
Tiered oversight proportionate to risk. Not every supplier warrants the same governance attention. An organisation with hundreds or thousands of suppliers cannot apply the same rigour to all of them. What it can do is apply meaningful rigour to the suppliers where a security failure would cause material harm: the suppliers with privileged access, with access to sensitive data, or upon whose services critical business functions depend. A tiered framework, with clear criteria for each tier and defined assurance requirements, allows the governance effort to be proportionate without being token.
Contractual standards that reflect actual risk. Security requirements in supplier contracts are often standard clauses that bear no relationship to the specific risk that supplier introduces. Effective third-party governance requires security terms that are calibrated to the risk: access controls, incident notification obligations (twenty-four hours is a common standard; forty-eight hours is too long for a critical supplier), audit rights, and the right to terminate without penalty following a material security failure. Legal teams that do not receive security input before contracts are negotiated routinely sign terms that create governance gaps.
Ongoing assurance, not point-in-time certification. A supplier that held an ISO 27001 certificate at the time of onboarding may not hold one now. Its security posture may have changed, its team may have turned over, it may have been acquired by an organisation with lower security standards. Governance requires ongoing assurance: annual reviews for critical suppliers, regular re-assessment of tiering decisions as the business changes, and a process for acting on assurance findings rather than filing them.
The board's specific role
The board's role in third-party risk governance is not operational. It is to ensure that the framework exists, that accountability for it is clear, that it is adequately resourced, and that the board receives sufficient information to understand whether it is functioning as designed.
That means at minimum: an annual review of the critical supplier inventory and the organisation's aggregate third-party risk position; a clear understanding of who is accountable for third-party risk governance and how that accountability is discharged; and a process for escalation to board level when a critical supplier poses a risk that cannot be managed within management's delegated authority.
The boards that get this right are not the ones with the most sophisticated third-party risk frameworks. They are the ones where the question is genuinely asked, repeatedly and seriously: who is responsible for ensuring our suppliers are secure, what does responsible look like in practice, and how do we know it is happening?
Ali Zeb is an Executive Cyber Security Advisor, Non-Executive Director, and former advisory member at the FCA, NCSC, and Lloyds of London Market Cyber Risk Committee. He advises boards and executive teams on cyber governance, third-party risk, and operational resilience.
Disclaimer
The views and opinions expressed in these articles are those of the author, Ali Zeb, and are provided for general informational and educational purposes only. They are based on professional experience, independent research, publicly available information, and the use of artificial intelligence tools to support analysis and content development.
While every effort is made to ensure the accuracy and relevance of the information presented, no representation or warranty, express or implied, is made as to its completeness, accuracy, or suitability for any particular purpose. The content should not be relied upon as professional, legal, regulatory, or financial advice.
Readers are encouraged to seek appropriate independent advice specific to their organisation and circumstances before making any decisions based on the information contained in these articles.
To the fullest extent permitted by law, the author accepts no liability for any loss, damage, or consequences arising directly or indirectly from the use of, or reliance on, the information provided.
Third-party risk on the board agenda?
The first conversation is about understanding your situation. I respond personally to every enquiry.
Arrange a Conversation